Architecting Borders: When Cloud Topology Must Obey National Law
The old promise of the cloud was global scale with a single control plane. Build once, deploy everywhere. That model is dead for anyone dealing with financial, healthcare, or government data. It wasn’t killed by technology limitations, but by a much older force: national borders. What began as “keep the data in Germany” has metastasized into a multi-jurisdictional puzzle where your application’s topology, the physical and logical arrangement of its components, is now dictated by legal statutes. The latency you once fought is now a compliance feature. The multi-region redundancy you deployed for failover is now a regulatory baseline. This is the new reality: geography is architecture.
Forget the abstract principles. The European Union’s executive branch is expected to present its “Tech Sovereignty Package” on May 27, 2026, which will include a range of measures aimed at bolstering the bloc’s strategic autonomy in key digital areas. Sources familiar with the talks have told CNBC that the package is expected to restrict member governments’ use of U.S. cloud platforms to process sensitive data, potentially impacting financial, judicial, and health sectors. This isn’t speculative. This is the near-term future where your AI strategy, or your ability to have one at all, depends on where your training data lived and where your models run. As a Forbes Council piece puts it: “Sovereignty is no longer just about where data lives. It now extends to where AI systems run, where models are trained and where inference occurs.” The era of convenient, centralized control is being replaced by a mandatory, fragmented, and legally enforceable multi-cloud, multi-region reality.
The False Promise of “Build Once, Deploy Anywhere”
For a decade, the goal was abstraction: treat the cloud as a global, fungible resource. Your VPC in us-east-1 was treated as logically identical to eu-central-1. Yet, the underlying physics and politics were always there, waiting to collect their due.
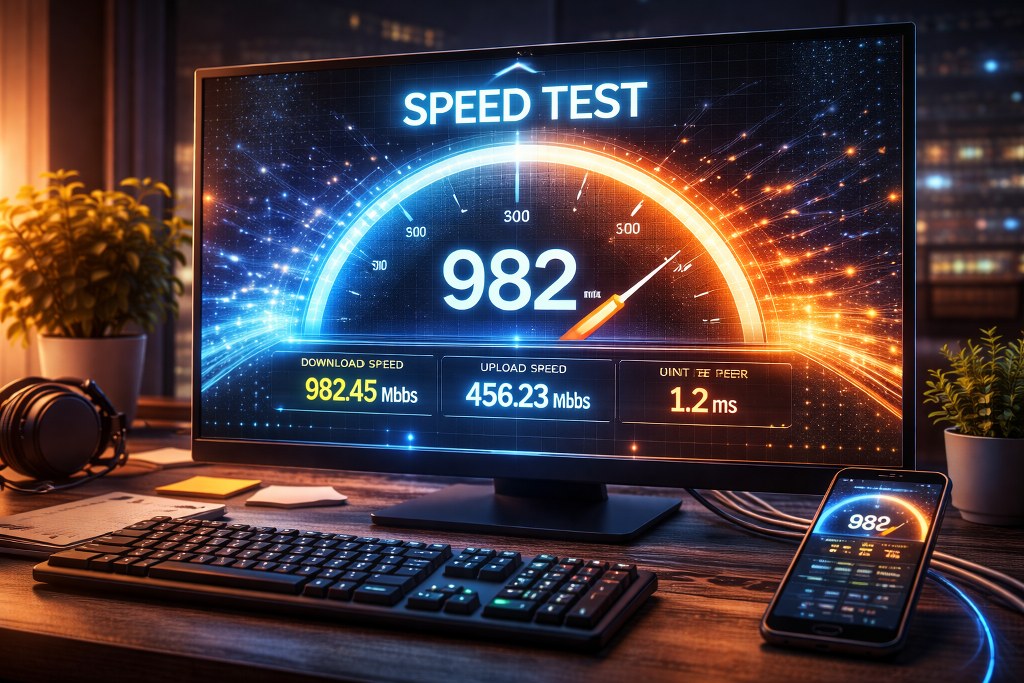
The practical friction is already measurable. Consider a simple European deployment. The latency between Amsterdam (europe-west4) and Frankfurt (europe-west3) is a mere 12-13 ms P50 round-trip time. Technically, you could treat them as a single failure domain. Legally, you cannot. Germany’s Federal Data Protection Act (BDSG) and France’s CNIL guidelines create distinct compliance silos.
The pain isn’t hypothetical. A developer migrating their entire stack off U.S. services found the process “real but manageable”, but noted the crucial trade-off: sovereignty for operational overhead. Moving from Google Analytics to self-hosted Matomo solved GDPR “cookie consent theater” but introduced server maintenance. Switching from SendGrid to the European service Lettermint meant simpler compliance but “leaner analytics.” Every step towards sovereign infrastructure is a step away from the seamless, integrated global platforms we’ve grown accustomed to.
This reality shatters the “deploy anywhere” dream. You aren’t choosing a region for latency or cost, you are choosing a legal jurisdiction. And as the AWS documentation on regions and zones implicitly warns: “Putting resources in different zones in a region reduces the risk… Putting resources in different regions provides an even higher degree of failure independence.” That “failure” now includes regulatory action.
Beyond Residency: The New Sovereignty Stack
Data residency, the where, was the first wave. The emerging challenge is operational sovereignty: control over the entire stack, from hardware access to software supply chains. The AWS Digital Sovereignty Pledge frames this as “customer control and choice across the AI stack”, a recognition that the ask has moved far beyond data location.
Let’s break down what this actually demands of your architecture:
1. Infrastructure Sovereignty:
The hardware must be in a compliant region, operated by entities bound by local law. The EU’s upcoming restrictions on U.S. cloud providers for sensitive government data is a blunt-force example. Your provider’s terms must contractually guarantee no extraterritorial access, a point AWS emphasizes by highlighting protections like the AWS Nitro System, which they claim is designed so that “there is no mechanism for anyone at AWS to access customer data.”
2. Processing Sovereignty:
This is the AI wildcard. Can a model trained on globally scraped data be used for inference on EU citizen data? Regulators are starting to ask. A model’s “provenance” becomes a new compliance vector. The Forbes analysis warns: “Enterprises relying on externally trained foundation models should be asking hard questions now about what data those models were built on. Regulators will eventually ask the same questions, and ‘we did not know’ is not a defensible answer.”
3. Network Sovereignty:
Data cannot traverse non-compliant jurisdictions. A user in Paris cannot have their API request routed through a U.S. load balancer, even if the final database is in Frankfurt. This kills the classic “global anycast” CDN pattern for authenticated traffic. Multi-region Shopify infrastructure guides now explicitly warn of the “pitfall” of “cross-traversing personal data to US infrastructure during processing.” Your traffic routing logic (Route53, Cloudflare Load Balancer) must become jurisdiction-aware.
4. Verifiability:
You must be able to prove all of the above. “Governance as provable infrastructure” is the new requirement. Immutable audit trails that track data lineage from ingestion through AI inference are no longer nice-to-have, they are the only defense in an audit.
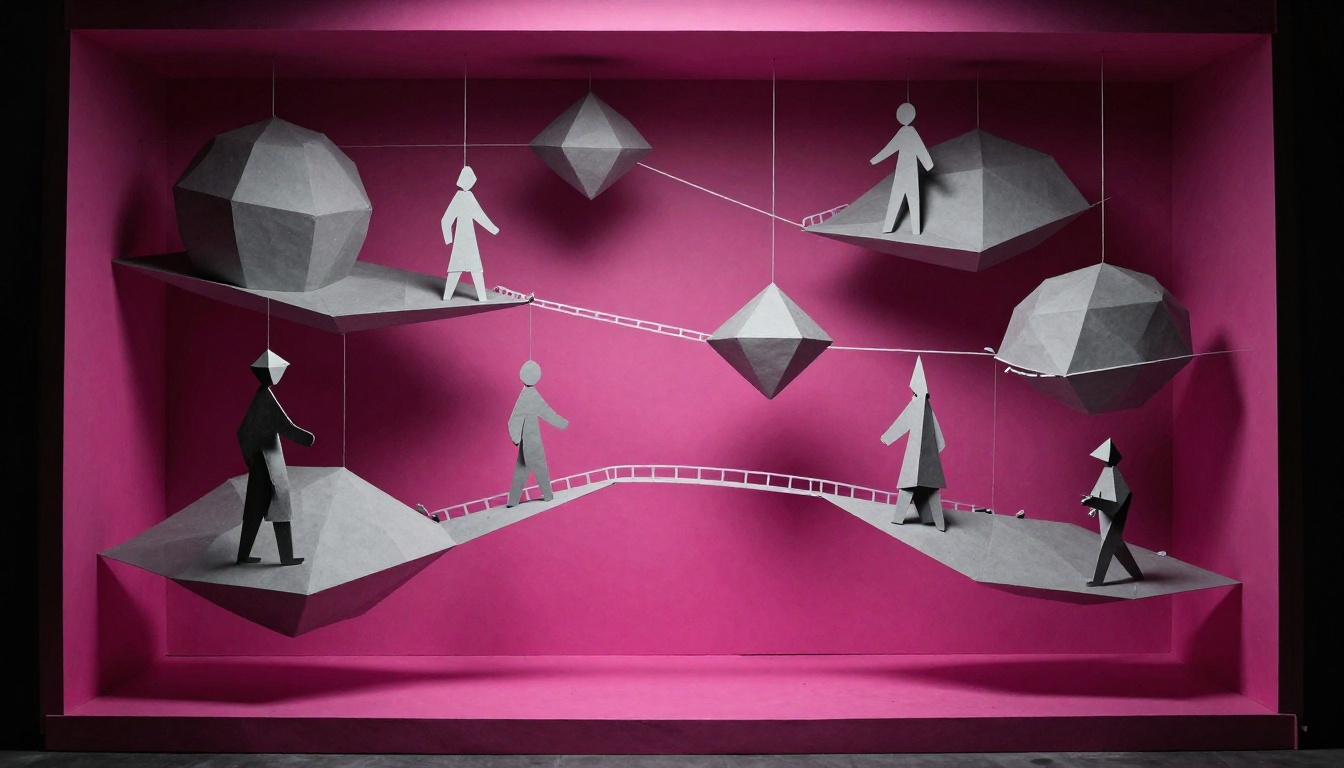
Blueprint: Architecting for the Balkanized Cloud
So, how do you build systems under these constraints? The principles of resilient, distributed systems, which many teams have neglected in favor of monolithic cloud convenience, suddenly become compliance mandates.
1. The Region-as-Service Pattern.
Stop thinking of eu-west-1 as just another AWS region. Treat it as a semi-independent deployment of your entire application stack, its own databases, caches, message queues, and compute. Each “regional service” is a full clone, designed for isolated operation. Service discovery and API gateways at the global edge direct traffic to the correct sovereign region based on the user’s determined legal domicile (not just geo-IP). This pattern forces you to confront the hard problems of distributed systems latency vs centralization trade-offs head-on, as you can no longer rely on a single, global control plane.
2. Jurisdiction-Aware Data Partitioning.
Your database sharding key is no longer user_id, it’s user_legal_jurisdiction. All data for EU citizens lives on EU-resident databases, with replication only to other EU regions for DR. This is the Azure Paired Region model applied to legal domains, not just fault domains. As their documentation states: for true BCDR, “each Azure region is paired with another region within the same geography.” Your disaster recovery pairing must now also be your compliance pairing.
3. Federated AI/ML Pipelines.
You cannot train a global model on a global dataset. Instead, you train regional “shadow models” within each sovereign boundary on local data. A global “consensus” or “orchestrator” model (hosted in a neutral or aggregating region) can then guide inferences, but the actual data and primary model weights never leave. This is the only viable path forward for regulated industries.
4. The Sovereign Edge.
Public CDNs sit outside your data boundaries. For serving static, public assets, this is fine. For authenticated sessions, personalized content, or API calls, you need an edge you control. This shifts the calculus for geopolitical sovereignty implications of edge infrastructure selection. Running your own edge nodes in-region, or using a provider with verifiable sovereign points of presence, becomes critical. The performance penalty of not using a global anycast CDN is now a compliance requirement you must engineer around.
The Cost of Sovereignty: More Than Euros
The bill for this architectural shift comes in multiple currencies.
-
Operational Complexity: Your
terraform applynow targets multiple cloud accounts or providers. Your observability stack must aggregate across legal boundaries without co-mingling logs. Incident response requires knowing which region’s laws govern the data involved in an outage. Teams need expertise in multiple regulatory regimes. - Performance Tax: The latency-optimized path is often the legally forbidden path. Directing a Milan user to the Frankfurt region for processing might be optimal (maybe 9ms latency to Frankfurt vs 19ms to Amsterdam for Swiss users), but if the processing involves personal data and your legal basis only covers Italy, you’re violating the architecture. Speed is subservient to law.
- Vendor Lock-in… to Sovereignty: Ironically, moving to “sovereign” European clouds like OVH, Scaleway, or dedicated AWS/Azure “sovereign cloud” offerings can create a new form of lock-in. These ecosystems lack the vast managed service catalogs of the hyperscalers. You trade control for capability, often rebuilding with more primitive IaaS components.
The Inevitable Future: From Exception to Default
Gartner projects that by 2027, 35% of countries will rely on region-specific AI platforms, up from just 5% today. The direction is unambiguous. The “global internet” is fragmenting into a network of bordered digital territories.
For architects, this means a fundamental shift in priority. The primary constraints are no longer just CAP theorem or latency budgets, they are Articles 44-50 of the GDPR, or China’s Data Security Law. Your system diagrams must now include not just availability zones, but legal jurisdictions. Your runbooks must reference not just error codes, but regulatory authorities.
The technical skills required are evolving. You need to understand not just how to deploy a Kubernetes cluster, but how to configure its etcd storage to never leave a geographic boundary. Not just how to train a model, but how to document its data lineage to satisfy a supervisory audit.
The cloud’s next decade won’t be defined by bigger regions or faster chips. It will be defined by how well we learn to build systems that are not just globally scalable, but legally coherent. To navigate this, you’ll need more than a cloud architect, you’ll need a sovereignty architect. Someone who can translate “Article 28 Processor Requirements” into a CrossTrafficPolicy Terraform module and understands that the most critical path in your system is no longer between your app and database, but between your data and the law. This is an era where the decisions around adapting system design for specific regulatory compliance standards will separate resilient, global businesses from those that are forced to retreat behind their own borders. The map is now part of the blueprint. Build accordingly.