When Imgur decided to block UK users from accessing its image hosting service, the company probably expected some grumbling but knew most people would move on. What they didn’t anticipate was tech-savvy users would simply build their own infrastructure to route around the damage. This creates an architectural irony: geo-blocking often triggers the exact user behaviors it was meant to prevent.
The reality is geo-blocking represents one of the most persistent anti-patterns in modern system design. It’s a blunt instrument that fails to achieve its goals while creating technical debt, security vulnerabilities, and unexpected business consequences. Let’s examine why this approach fails and what happens when technical controls meet determined users.
The Imgur Incident: From Inconvenience to Architectural Rebellion
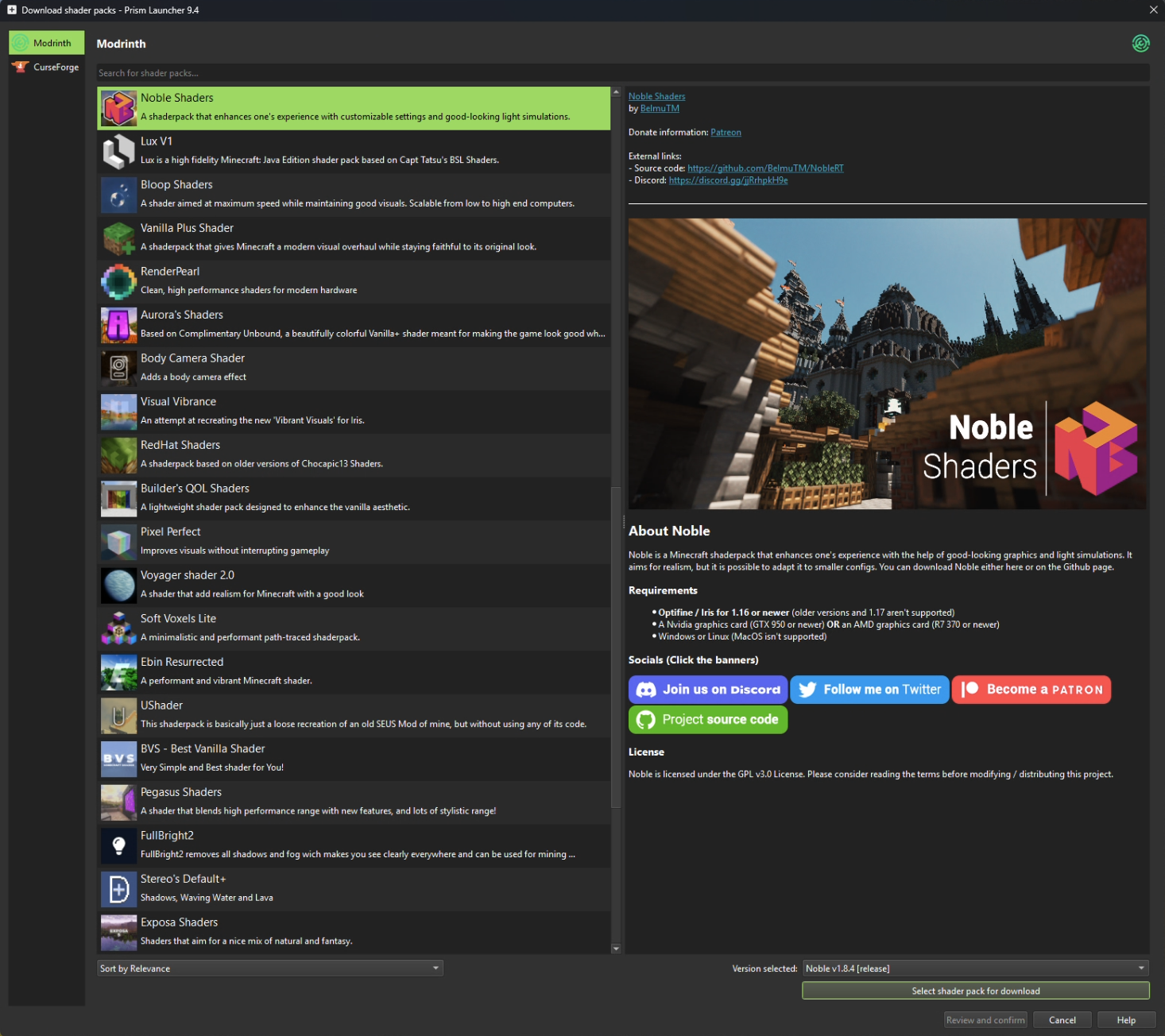
When Oscar Molnar found himself unable to view Minecraft shader previews because Imgur images were unavailable in the UK, his solution wasn’t to complain – it was to architect. His home network approach bypassed Imgur’s restrictions through a clever combination of Pi-hole DNS interception, Traefik routing, and VPN tunneling using Gluetun containers.
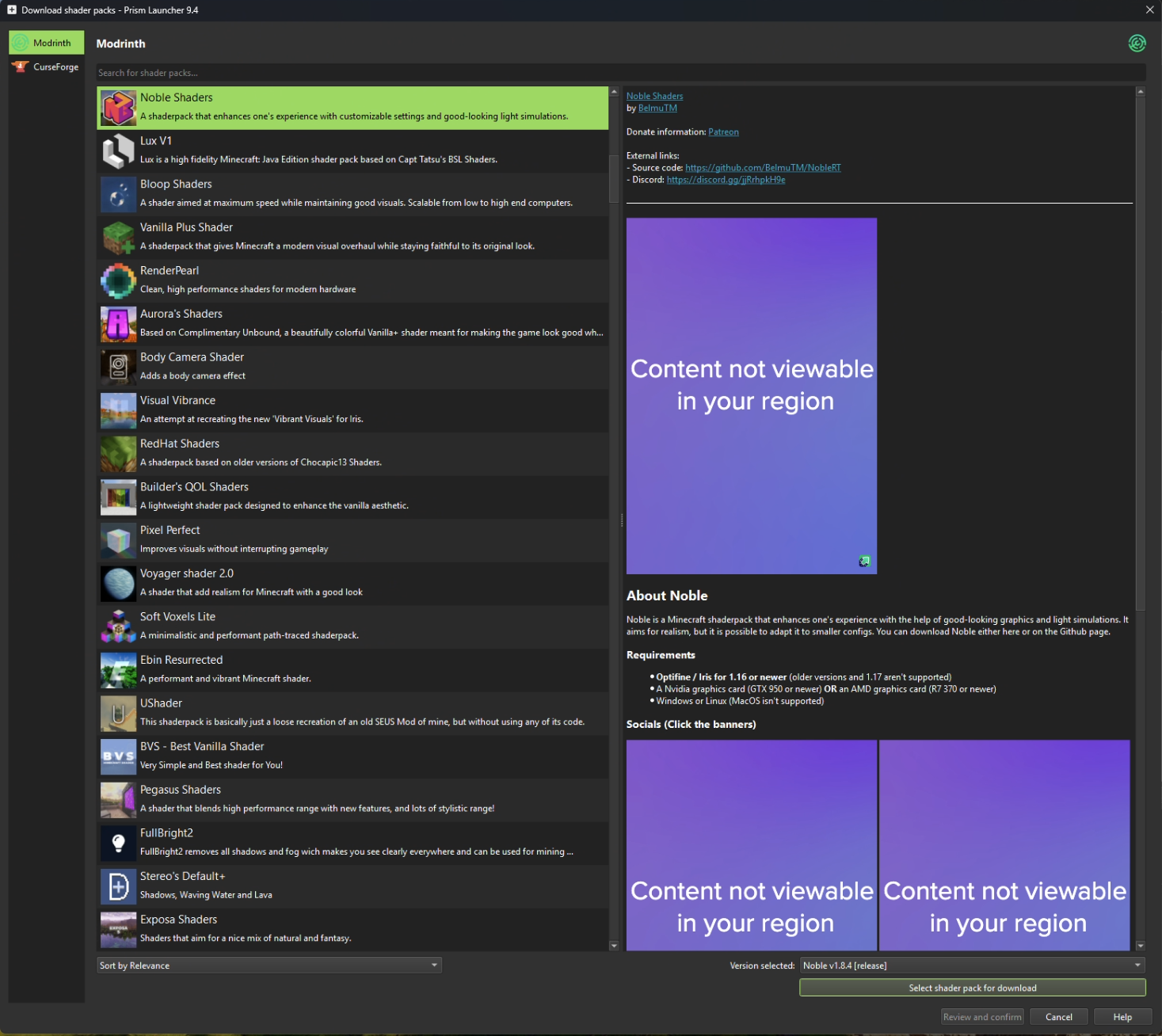
The technical implementation was elegant: DNS queries for i.imgur.com get redirected to his Traefik instance, which forwards connections through a VPN-connected Nginx container. As Molnar noted, “Now when any device on my network requests an Imgur image, it works. My phone, my laptop, guest devices, everything. No VPN apps to install, no browser extensions, no manual configuration.”
This individual-level solution reveals the fundamental flaw: when legitimate users must build proxy infrastructure to access content, the blocking mechanism has failed its core purpose.
Why Geo-Blocking Creates More Problems Than It Solves
At surface level, geo-blocking seems like a straightforward technical solution to legal compliance requirements. The Indian government’s Online Gaming Act, 2025 demonstrates this thinking, attempting to prevent offshore gambling platforms from serving Indian players through location-based restrictions. But the limitations of these technical controls become apparent quickly.
VPNs and proxies render geo-blocking ineffective for motivated users. As the research explains, “Any geo-blocking restriction can be bypassed through the use of ‘virtual private networks’ (VPNs), thereby resulting in the rise of grey market prominence.” The same tools people use to watch Netflix shows from other countries work equally well for accessing blocked gambling sites or, in Imgur’s case, simple image hosting.
The technical methods themselves are fundamentally fragile:
- IP-based filtering relies on commercial geolocation databases that are often inaccurate or delayed when address blocks get reassigned
- DNS-level blocking gets bypassed through alternative resolvers or direct IP connections
- Transport-layer inspection becomes an arms race against adaptive evasion techniques
- Device-level checks raise privacy concerns and get defeated by privacy-focused browsers
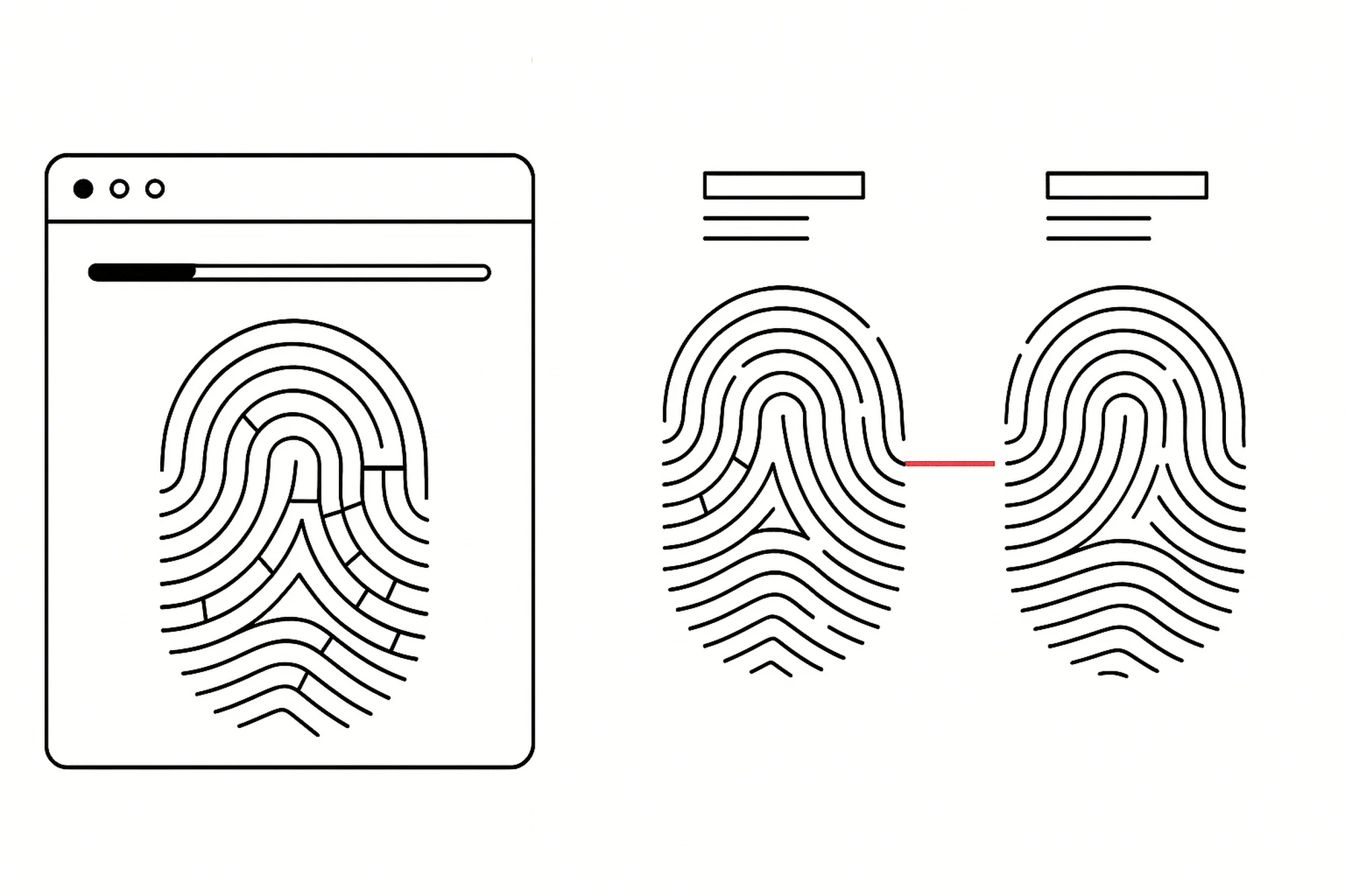
Modern detection systems expose the depth of the challenge. As noted in the Gologin analysis, “Changing the User-Agent alone doesn’t reset your browser footprint… sites see many characteristics of your software (your device ID, browser fingerprints, cookies) and can easily link two accounts to each other based on these patterns.” Yet even these sophisticated systems can’t stop determined bypass attempts.
The Ripple Effects: When Blocking Creates Security Vulnerabilities
The most dangerous consequence of geo-blocking isn’t the bypassing itself – it’s the architectural consequences that emerge from user-driven workarounds.
When legitimate users like Molnar implement their own proxy solutions, they’re essentially creating shadow IT infrastructure. While his specific implementation appears secure, not every user has the technical expertise to build robust systems. The result is often poorly configured proxies, insecure VPN connections, and malware-infected “free proxy” services that users turn to when simple access is blocked.
This creates a perverse incentive structure: by making legitimate access difficult, platforms encourage users toward riskier alternatives. The Gologin research highlights this concern, noting that “Free VPN services, shared proxies or booster extensions are very often under strict eye of security systems on most websites and social networks. This can also include cheap datacenter proxies. Trying to hide many accounts behind datacenter proxies will inevitably result in all your accounts restricted.”
The architectural problem becomes circular: platforms implement blocking to comply with regulations, users implement workarounds that create security risks, platforms implement more sophisticated blocking, and the arms race continues.
Better Alternatives: Beyond the Binary Block
If geo-blocking is fundamentally flawed, what should replace it? The lessons from supply chain integrity provide a more sophisticated framework. As the Supply Chain Game Changer analysis notes, “Effective supply chain integrity relies on layered controls that combine identification, trusted credentials, provenance information and continuous monitoring, and the same layered approach can strengthen digital market regulation.”
Rather than blunt blocking, modern approaches should focus on:
Context-Aware Access Controls
Instead of binary allow/deny based on location, systems can implement gradient access. Maybe users from restricted regions can view content but not upload, comment, or share. Perhaps they see a limited feature set rather than complete denial. This maintains compliance while reducing the incentive for bypass.
Payment Channel Enforcement
As the gaming regulation research suggests, “regulation of online gambling can benefit from focusing on financial flows through payment processors, app stores and advertising platforms, which limits profitability even when access remains technically possible.” Cutting off the money flow is often more effective than cutting off the content flow.
Provenance and Identity Verification
Modern identity systems allow for verified access without complete blocking. Digital signatures, blockchain verification, and trusted platform modules can create assurance about user identity and compliance status without resorting to geographic restrictions.

The Unintended Consequences for Content Delivery Networks
The architectural impact extends beyond individual platforms to the entire content delivery ecosystem. When users implement workarounds like Molnar’s DNS-level interception, it creates traffic patterns that CDNs aren’t designed to handle.
Content delivery networks rely on geographic routing to optimize performance. When users proxy through other countries, they break these optimizations, potentially increasing latency and bandwidth costs for both users and providers. The very infrastructure designed to make content delivery efficient gets subverted by the bypass mechanisms users implement.
Beyond performance impacts, this creates monitoring blindspots. Platforms lose visibility into their actual user distribution and engagement patterns when significant traffic gets routed through proxy networks. This distorts analytics, undermines A/B testing, and makes capacity planning more difficult.
The Future: From Blocking to Understanding
The fundamental shift needed is psychological rather than technical. Instead of asking “how can we block users from restricted regions?”, we should ask “how can we serve users while maintaining compliance?”
This means designing systems with geographic restrictions as a feature rather than an afterthought. It means building in graceful degradation rather than hard walls. It means recognizing that technical controls will always be circumvented and planning accordingly.
As platforms increasingly operate in a global context with conflicting regulations, the brute-force approach of geo-blocking becomes increasingly untenable. The architects designing tomorrow’s systems need to learn from the failures of today: users will route around damage, and fighting that reality is a losing battle.
The lesson from the Imgur incident isn’t that we need better blocking technology. It’s that we need better system design that accounts for human ingenuity and the limitations of technical controls. When your users are building their own infrastructure to bypass your restrictions, maybe the problem isn’t with the users – it’s with the restrictions.
The next generation of content delivery and access control systems will succeed by embracing flexibility rather than fighting it. They’ll implement smart, context-aware controls rather than brittle geographic walls. And they’ll recognize that in a connected world, the best way to control access isn’t to build higher walls – it’s to build better doors.