Your Password Manager is the Browser Itself
You encrypt your passwords at rest. You toast to your encrypted vault in transit. But unless you’ve designed for security in memory, you’re leaving the back door wide open. A recent incident involving Microsoft Edge, reportedly storing passwords in memory in plaintext, isn’t just a bug, it’s a stark illustration of our collective blind spot. We’ve built cathedrals of encryption around data at rest, while a simple pointer error can spill the secrets of the entire congregation onto the floor.
This isn’t an isolated failure. It’s a systemic symptom of prioritizing performance and convenience over secure state management patterns. Let’s move beyond the headline and dissect what this really means for architects building systems that handle humanity’s most sensitive data.
Beyond the Edge: The Porous Memory State
While the specifics of the Edge incident are still under wraps, the core allegation is devastatingly simple: passwords, the crown jewels of digital identity, were reportedly held in RAM without encryption while the browser was active. This bypasses every sophisticated storage encryption scheme. An attacker with local code execution or a cold-boot attack now has a direct tap into the clear-text stream.
This vulnerability sits at the intersection of two critical architectural failures:
The Illusion of Ephemerality
We treat runtime memory as a “scratchpad”, assuming it’s transient and therefore safer. But memory dumps, debugging tools, process introspection, and cold-boot attacks turn this ephemeral space into a permanent record.
The Performance-Guilt Trap
Encrypting and decrypting data in memory for every access costs CPU cycles. In the high-stakes performance arena of browser rendering, such overhead is often deemed unacceptable. Security loses to the 60fps scroll.
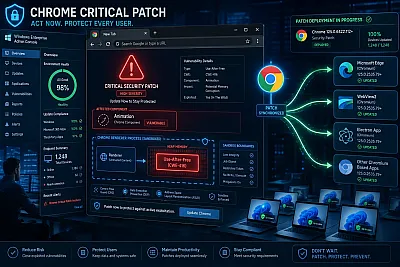
The industry’s response to this class of problem has been a frantic game of whack-a-mole. Look no further than the recent Google Chrome 147.0.7727.138 release, which patched a staggering 30 memory-safety vulnerabilities in a single update. The table of patched CVEs reads like a tour of Chrome’s attack surface:
| Component | CVE | Type | Impact |
|---|---|---|---|
| WebMIDI | CVE‑2026‑7350 | Use-after-free | Sandbox escape |
| Canvas | CVE‑2026‑7363 | Use-after-free (Critical) | Sandbox bypass |
| Accessibility | CVE‑2026‑7344 | Use-after-free (Critical) | Sandbox bypass |
| Views UI | CVE‑2026‑7343 | Use-after-free (Critical) | Sandbox escape |
| ANGLE | CVE‑2026‑7359 | Use-after-free | Sandbox escape |
These aren’t obscure features. This is Canvas rendering, the UI layer, the audio stack, core components. Each “use-after-free” is a potential pointer mishap where freed memory, potentially containing sensitive data, is incorrectly accessed and could be manipulated by an attacker. If these subsystems can be compromised to leak their own data, what hope do ad-hoc password buffers have?
The Architectural Consequences of Forgetting Memory
The password-in-memory flaw forces a confrontation with uncomfortable architectural truths.
The Browser as a Monolithic Root of Trust
A modern browser is a de facto operating system. It handles rendering, networking, media, execution (WASM/JS), and now, with password managers and payment autofill, acts as a trusted credential vault. When the vault’s security depends on the integrity of every other component in the monolithic process, from the PDF renderer to the WebMIDI API, you’ve created a system where the attack surface is the sum of all its parts. The sheer number of recent high-severity flaws in browser components proves this model is untenable.
State Management is a First-Class Security Concern
We have patterns for storing data (databases, files) and patterns for transmitting data (TLS, encryption). We lack mature, widely-adopted patterns for handling sensitive state in active memory. Should passwords be pinned to a secure enclave (like Apple’s Secure Enclave or Intel SGX) even during entry and autofill? Should the password manager function run in a process with vastly reduced privileges, isolated from the rest of the browser’s sprawling code? These are architectural questions, not library choices.
The Lingering Process Problem
As noted in the Chrome update analysis, there’s an operational chasm between patching and protection. Updates are staged silently, but “until a browser restart occurs, the vulnerable process continues to run.” This means an enterprise machine, auto-updated overnight, remains exposed to any in-memory data leak until the user reboots the application. For systems that run 24/7, this creates a dangerous window.
Building Systems That Don’t Betray Their Own Memory
So, what do we do? The path forward isn’t just about fixing one browser bug, it’s about adopting a new mindset for secure state management.
1. Adopt Memory-Safe Languages
The most effective way to eliminate entire classes of memory-safety vulnerabilities (buffer overflows, use-after-free) is to stop using languages that allow them. The industry shift is underway. For instance, the strategic adoption of memory-safe languages like Rust to reduce vulnerability density is a direct response to this crisis. Critical components handling sensitive data should be the first candidates for rewriting or isolation within memory-safe boundaries.
2. Enforce Process Isolation
The principle of least privilege must extend into runtime. The component responsible for credential management should operate in the most sandboxed, minimal process possible, communicating via rigorously defined, capability-secure IPC channels. This limits the blast radius if any other part of the system is compromised.
3. Design for “Memory Amnesia”
Sensitive data should have the shortest possible lifespan in clear-text memory. Architect for zeroization, actively overwriting memory buffers, immediately after use. Avoid holding entire credential databases in RAM, instead, fetch, decrypt, use, and zeroize individual entries on-demand.
4. Treat Browser Updates as Critical Infrastructure
The scale of the recent Chrome patch, 30 fixes, shows this is no longer “application maintenance.” It’s infrastructure security. Organizations must streamline browser restarts as part of the patch cycle, treating the browser with the same urgency as the OS kernel.
The Takeaway: From Storage Vaults to Secure Pipelines
The Edge incident is a canary in the coal mine. It exposes the fallacy of securing only the start and end points of data’s journey. In the modern software stack, the journey itself, through the complex, bug-riddled landscape of application memory, is the most dangerous leg.
As architects and developers, we must evolve our thinking. Security isn’t a feature you bolt onto storage, it’s a property you must design into the entire lifecycle of data, especially during its most vulnerable state: when it’s being actively used. This requires embracing memory-safe foundations, re-architecting for ruthless isolation, and treating runtime memory not as a safe scratchpad, but as hostile territory. The next frontier of security won’t be won with better vaults, but with architectural resilience and debugging race conditions during production incidents. It’s time to start building systems that are not only clever, but also forgetful in all the right ways.

